Articles in Category: Internet
The Internet – the global network of networks and one of the most significant and powerful things to have come along ever.
How Do I Fix “Internal Server Error”?
An Internal Server Error happens within the server attempting to show you a webpage. It’s usually a server-side problem out of your control.
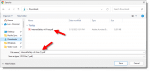
How Do I Download All OneDrive Files to My PC?
Downloading all your OneDrive files isn’t particularly difficult; it’s just not particularly obvious. I’ll show you two ways to do it.
Is There a Way to Use OneDrive as a Dumb Hard Drive?
Yes, you can use OneDrive online without using OneDrive on your PC or going to OneDrive.com. I’ll show you how.
Should I Accept Cookies On My Computer?
You’ll be asked again and again whether or not a site can leave cookies. I’ll explain why, what the ramifications are, and my suggested answer.
Why Do Ads Follow Me Around the Internet?
Advertising networks notice what interests you. It might be a little creepy, but it’s not malware.
How Do I Backup OneDrive Files?
You shouldn’t rely on OneDrive as the only place for your files. Backing them up elsewhere is important, but there may be bumps in the road.
How Do I Get Rid of OneDrive?
Some people just want it GONE. I’ll show you how to get rid of OneDrive.
Is Private Browsing Really Private?
Incognito, Private, or In Private modes protect your privacy to a point. It’s critical to know where that point is.
How to Send a Fax From Your PC
Sending a fax is less and less common, but as it turns out, it’s also very easy.
What Is “about:blank” (or “about:blank#blocked”) and How Do I Get Rid of It?
About:blank is a special blank page in browsers that appears due to problems, malware, or malware removal. It can also be a useful home page.
What Is a Browser Cache? How Do I Clear It?
Clearing your browser cache is the first thing to try when you encounter webpage problems. I’ll look at why and how to clear your cache.
How Websites Remember You: Diving into Cookies & More
Websites remember that you signed in previously both as a convenience and as a way to make using the site possible.
Do Multiple Browser Processes in Task Manager Slow My Computer?
Multiple instances of your browser showing in the task manager is not a problem — it’s how browsers work. It’s the total RAM usage you should pay attention to.
7 Things Your Sysadmin Probably Won’t Tell You
If you run a website and have someone administering it for you — a system administrator or “sysadmin” — they may have much more power than you realize.
What Can I Do If Someone Uses My Credit Card Online?
Using someone else’s credit card online illegally is identity theft. There’s not a lot you can do except report it.
What Is JavaScript and Why Do I Need It?
JavaScript is a programming language that operates important features on many websites.
How Do I Delete and Reinstall Microsoft Edge?
Since Edge is a component of Windows itself, uninstalling it isn’t an option. I’ll review alternatives to help resolve Edge problems.
If I Leave a Service Like LastPass, Does My Data Remain Online?
When you leave a service, or if your information is stolen from that service, there may be steps you need to take.
How Do I Get Rid of Edge in Windows 11?
Edge is essentially impossible to remove. I’ll review the choices you have.
Will Google Delete Inactive Accounts?
Google is changing their account inactivity policy. This may have some serious ramifications, but it’s easy to keep your account from being deleted.
The Problem With OneDrive Backup
OneDrive’s backup function is broken. I’ll explain why and what to do about it.
How to Change the Default Search Engine in Microsoft Edge
It is possible to change the default search engine in Edge; it’s just not obvious and sometimes ineffective.
Why Doesn’t “Back” Always Work?
Occasionally, the back button won’t work and simply lands you back where you were. There are reasons, and there are workarounds.
How Do I Get an Old Version of a Webpage?
It’s generally not possible to recover an older version of a webpage, but we’ll look at a couple of straws to grasp at.
What Is Podcasting?
Podcasting delivers periodic or serialized audio content to your portable devices and other players.
Don’t Be Fooled By Ads
Advertisements support the free information available online. It’s critical that you can distinguish ads from genuine content.
What’s the (Number) Added to Some of My Downloads?
Your browser may add a number to your download’s file name to avoid collisions if you download a file of the same name more than once.
Just What Is Common Sense?
‘Common sense’ is frequently suggested, often missing, and rarely defined. I’ll take a look at some of what I feel are the characteristics of common sense.
Is Using the Cloud Safe?
As security compromises seem to happen regularly, many ask, “Is using the cloud safe?” It’s as safe as you make it.
Is My Information Safe in the Cloud?
‘The cloud’ is the latest buzzword for internet-based services. It’s important to understand a few things about cloud security.
Why Are There Sites in My History I’ve Never Been To?
Occasionally, sites appear in your browser history that you never visited. I’ll examine some possible causes.
How Do I Download a YouTube Video Transcript?
Transcripts can capture information from video and audio sources. YouTube makes downloading a transcript fairly easy.
Is OneDrive a Backup?
OneDrive is a powerful tool, but thinking of it as a backup can take you down a dangerous path.
What Should I Do About Boxcryptor?
With its sale to Dropbox, the future of Boxcryptor is uncertain. There’s no rush to take action, but I’ll share recommendations.
How Do I Switch From Edge to Chrome?
It’s easy to start using the Chrome internet browser instead of Edge, and I’ll show you how. Unfortunately, Edge may still make occasional appearances.
Two Steps to Better Search Results
Searching the internet is an art of sorts. I’ll share my two-step approach to better search results.
Where Do Cookies Come From?
Cookies are a fact of life when browsing the web. But if you look at the cookies stored on your machine, you might be surprised how many there are.
Five Reasons I Went All-in With Dropbox
Knowing how you use online storage will help you choose the correct provider with the correct set of features at an appropriate price.
How Do I Find Out When a Webpage Was Created?
It’s surprisingly difficult to tell with certainty when a webpage was written. There are some clues we can gather that might help a little.
The Most Searched-for Term on the Internet
The most searched-for term on the internet tells us something about people’s understanding (or lack of understanding) about how browsers and the internet work.
How Do I Clear Cookies for One Site?
Clearing all cookies can be painful. Fortunately, it’s also possible to clear cookies one site at a time.
Half a Dozen Uses for OneDrive
OneDrive is a surprisingly powerful service that many people overlook or don’t understand. I’ll review six ways you can leverage OneDrive.
How Can One Service Take Down So Much?
What happens when a major cloud service goes down, and what’s the takeaway?
What’s a QR Code?
QR codes are a nifty way to encode web addresses and other text in a way that’s easy for your smartphone to decode, but they are not without risk.
How Do I Search a Site That Has No Search Box?
Many sites lack a search facility. Fortunately, it’s easy to do it yourself using a search engine like Google. Even when sites provide their own, this do-it-yourself solution may give you better results.
Why “Always Keep on this Device” Doesn’t
The “Always keep on this device” feature has misled people into deleting and losing important files. Here’s why, and what to do instead.
Why Is My OneDrive Full?
OneDrive tries to make it easy to back up important folders, but at the cost of making some things very confusing.
What is RSS, and Why Should I Care?
RSS is a powerful information-publishing and -collection mechanism that bypasses email and makes it easy to stay up-to-date with a large number of websites and other RSS-enabled services.